As with most of the other VMware View 5.0 roles, deploying the Security Server role isn’t all that exciting (the excitement or frustration comes when configuring the firewall rules) so this post serves to show what the deployment looks like and I’ll proceed to write another post on a sample configuration at a later time.
The installation of the Security Server role in VMware View 5.0 isn’t a whole lot different than 4.5 so in case you’re not aware of it, there is actually a VMware publicly published KB with a video tutorial that shows the deployment process:
Installing and configuring the VMware View 4.5 Security Server
http://kb.vmware.com/selfservice/microsites/search.do?language=en_US&cmd=displayKC&externalId=1030298
One of the common questions I’m sure most engineers would ask is whether the security server should be dual homed (2 x NICs) or single homed (1 x NIC) since it’s supposed to sit in the DMZ. While the article is a bit older (3.x and 4.0.x), I believe it still applies:
Using Windows Firewall and Dual Network Interface Cards with VMware View Servers
http://kb.vmware.com/selfservice/microsites/search.do?language=en_US&cmd=displayKC&externalId=1024610
There are also Reference Architecture documents publicly available from VMware such as the following for version 4:
VMware View
A Guide to Large-scale Enterprise VMware View 3 and VMware View 4 Deployments
http://www.vmware.com/files/pdf/resources/vmware-view-reference-architecture.pdf
Prerequisites
The following are the prerequisites you should prep the server with:
- Make sure that Remote Desktop Services (RDS) / Windows Terminal Server Role is not installed.
- Configure the Security Server with 1 NIC.
- Assign the Security Server with a port group in your DMZ network.
- Prepare a security server pairing password by configuring one on the View Connection server.
- Work with your network engineer to prepare the firewall rules between the internet, DMZ and internal trusted network: http://kb.vmware.com/selfservice/microsites/search.do?language=en_US&cmd=displayKC&externalId=1027217.
Once you’ve completed prerequisites 1 through 3, proceed with creating the security server paring password which is a one-time password that permits a security server to be paired with a View Connection Server instance by logging into VMware View Administrator, navigate to View Configuration –> Servers, select your View Connection Server, click on the More Commands button and select Specify Security Server Paring Password…:
Type in a paring password:
Note that you can select either Minutes or Hours for the Password timeout value:
Selecting OK will bring you back out to the administrator webpage:
Note that depending on how you configure the network for your security server, you may need to add entries into your Security Server’s host files to resolve the View Connection that is sitting in your trusted network.
Once you have the prerequisites configured, proceed with logging into your security server and launch the View installation file:
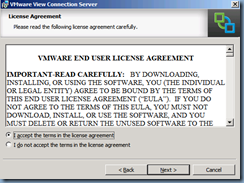
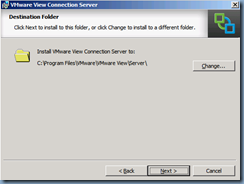
Proceed through the installation wizard:
In the Installation Options step, select View Security Server:
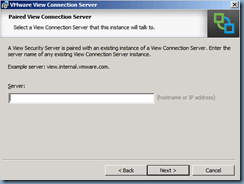
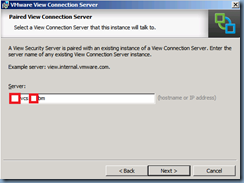
In the Paired View Connection Server step, enter the hostname or IP address of your internal View Connection server:
**Note that as I mentioned previously, if you’re not using your internal DNS servers for your Security Server, you’ll need to add an entry in the host files for your View Connection server if you choose to use the hostname. Also make sure that you use the FQDN for the hostname and not a NetBIOS name.
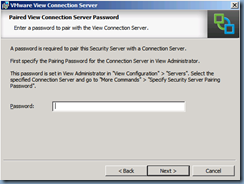
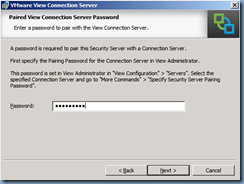
Enter the pairing password you’ve previously configured:
Enter the appropriate External URL (what your users will use to access their virtual desktops from the internet) and the PCoIP External URL IP (what the public IP mapped to the external URL is):
Proceed through the wizard to continue the install:
Once the install completes, proceed with switching back to the VMware View Administrator console and you should now see the new Security Server listed under the Security Servers table:
Note that you can edit the External URL and PCoIP External URL fields if you made a mistake during the install by selecting the security server and clicking on the Edit button:
There you have it. The Security Server has been installed.





















No comments:
Post a Comment