I’ve come across a few posts about the changes to an Active Directory computer object when you disjoin and rejoin it from the domain and have found many mixed answers and interpretations. There were also times when I find myself struggling to remember the details of how some components of AD works and since I was recently called about a problem that could be solved by a disjoin and rejoin operation for a computer object in the domain, I thought I’d write a post about the differences between resetting a computer object and deleting a computer object as it pertains to the changes to the Active Directory GUID and SID.
To illustrate the differences between resetting a computer object: http://terenceluk.blogspot.com/2011/02/trust-relationship-between-this.html
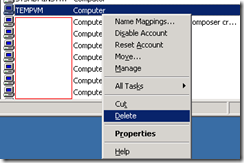
… and deleting a computer object:
… let’s use the following problem I wrote about in a previous post as an example:
In this situation, we have just virtualized a server but since the physical server was live cloned and the computer password age between the domain controller and the server itself has expired, the password was changed and we are no longer able to use domain accounts to log onto the server.
Most administrators know that every computer in Active Directory is assigned a GUID (Globally unique identifier) and subsequently a SID (Security ID) when it is joined to the domain and sometimes having these unique identifiers changed can wreck havoc to the applications hosted by the server. I find that most people think that by disjoining and rejoining the server to the domain, the operation will change both identifiers. This is actually not the case depending on which way you choose to handle the computer object in Active Directory. To illustrate this, I’ll show what happens with a simple test:
Resetting the computer account:
If you choose to use the Reset Account option within Active Directory Users and Computers, you will actually retain the GUID and SID for the computer object because the object was never deleted from Active Directory. Here’s an example of what I did:
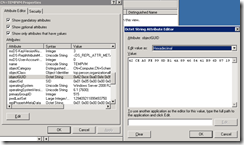
Screenshot-ed the objectGUID and objectSid attributes of the computer object in ADSIedit:
Went ahead and reset the computer account, disjoined server from domain, rejoined to domain. When you open up the windows as shown above with ADSIedit, you’ll notice that the GUID and SID doesn’t change.
Deleting the computer account:
If you choose to use the Delete option within Active Directory Users and Computers, you will actually create a new GUID and SID for the computer object because the complete new object was created and therefore Active Directory would have assigned a new GUID and SID. Here’s an example of what I did:
Screenshot-ed the objectGUID and objectSid attributes of the computer object in ADSIedit:
Went ahead and reset the computer account, disjoined server from domain, rejoined to domain. When you open up the windows as shown above with ADSIedit, you’ll notice that the GUID and SID are no longer the same:
This doesn’t necessarily mean a disjoin and rejoin operation won’t render an application on the server unusable but this illustrates that the GUID and SID won’t change as long as you do not delete the object.
For more information about SIDs and GUIDs, see the following:
How Security Identifiers Work: http://technet.microsoft.com/en-us/library/cc778824(WS.10).aspx
SID vs. GUID: http://technet.microsoft.com/en-us/library/cc961625.aspx








No comments:
Post a Comment