I’ve received a few messages over the past few months to ask whether I’ve written a blog post to update two of my previous posts:
Configuring for ICA Proxy with Citrix NetScaler VPX (1000) 10 and XenApp 6.5
http://terenceluk.blogspot.com/2012/10/configuring-for-ica-proxy-with-citrix.html
Configuring Citrix NetScaler VPX (1000) 9.3 for publishing Web Interface server access by authenticating against Active Directory
http://terenceluk.blogspot.com/2012/02/configuring-citrix-netscaler-vpx-1000.html
As I’ve been traveling over the past 2 months, I never got the chance to do so but now that I’m back, I’ve put this as one that I’d write as soon as possible. Before I begin, please note that the configuration I’m about to demonstrate was simply done through reading Citrix eDocs and a bit of trial and error. I need to state that I am not a NetScaler expert but I know just enough to get by. Please forgive any mistakes I may have made.
With that out of the way, let’s get this started.
Product Versions
NetScaler VPX
Version: NS10.1
Build: 124.13.nc
Date: Feb 20 2014, 18:53:27
XenDesktop
Version: 7.1
Prerequisites
This blog post will not go into the details of System configuration of the NetScaler but I’ll include screenshots of what configuration used in this example looks like.
System Configuration
IP Addresses
The following are the assignments for the NSIP (NetScaler IP), SIP (Subnet IP) and VIP (Virtual IP) addresses:
NetScaler IP: 172.16.2.10 – Management for NetScaler node 1
Subnet IP: 172.16.2.12 – SIP for NetScaler node 1
Virtual IP: 192.168.50.8 – VIP for NetScaler Gateway Virtual Server accessed by internet traffic
Virtual IP: 172.16.2.20 – VIP for NetScaler Gateway Virtual Server accessed by internal network
Virtual IP: 172.16.2.21 – VIP for NetScaler Load Balance Virtual Server
Network Routes
As the design of the NetScaler VPX appliance will be dual-homed, routes to the various internal network subnets will need to be configured as shown in the following screenshot:
High Availability Pairing
While it is optional, if you have HA configured for the NetScaler, ensure that the high availability pairing is in good health as shown in the following screenshot:
Publishing XenDesktop 7 StoreFront on a NetScaler VPX
Traffic Management Configuration
Configure Servers
The purpose of configuring the Servers node is to specify the XenDesktop 7 StoreFront servers in the environment. Navigate to Traffic Management --> Load Balancing --> Servers:
Click on the Add… button to open the Create Server window and fill in the following:
Server Name: <A name to identify the StoreFront server>
IP Address: <The IP address of the StoreFront server>
Repeat the same procedure for the second StoreFront server:
Note the 2 server objects created are now listed in the window:
Configure Services
The purpose of configuring the Services node is to define the service or services that the server objects will provide and allow the NetScaler appliance to monitor the service up/down state. The StoreFront servers will be delivering HTTP connectivity so we’ll configure the service by navigating to Traffic Management --> Load Balancing --> Services:
Click on the Add… button to open the Create Service window and fill in the following:
Service Name: <A name identifying the server and service>
Server: <Select the server created in the previous step>
Protocol: HTTP
Port: 80
Leave the rest of the settings as the default and a tcp-default with a Weight of 1 will be automatically configured for the service.
Note the new service created in the state and the State listed as being up:
Repeat the same procedure for the second StoreFront server:
Note that the second StoreFront service is now displayed:
Opening the properties of the service will that a monitor for tcp-default with a Weight of 1 will be automatically configured for the service:
Configure Load Balanced Virtual Servers
With the Servers and Services nodes configured, we can now use these objects to configure a virtual server object representing the two StoreFront servers and the HTTP service they provide. This virtual server will automatically load balance the two StoreFront servers and forward traffic to them if the HTTP service is up. Navigate to Traffic Management --> Load Balancing –> Virtual Servers:
Click on the Add… button to open the Create Virtual Server (Load Balancing) window and fill in the following:
Check the checkboxes under the column labeled Active:
Click on the Method and Persistence tab and change the Persistence setting from NONE to SOURCEIP:
Click on the Create button to create the load balanced virtual server:
Note that the new load balanced virtual server is now created with the State listed as being up:
All traffic directed to this load balanced virtual server will be split between the two StoreFront servers with the consideration of whether they are accepting HTTP requests. In the event that the server does not accept HTTP requests, the server will be deemed as being down.
Configure HTTP to HTTPS Redirect
It is recommended to configure a HTTP to HTTPS redirect because this would allow users to access the site via HTTP while getting redirected to HTTPS so their credentials are secured. Since the NetScaler will have one IP for users connecting from the internet and one IP for users connecting from the internal corporate network to access the portal, we’ll need two virtual server objects created to redirect requests for the two IPs. To configure the redirects, navigate to Navigate to Traffic Management --> Load Balancing --> Virtual Servers, click Add… and fill in the following:
Name: <A name identifying the redirect for the external virtual server>
IP Address: <The IP address that will be assigned to the external virtual server>
Leave the rest of the settings as the default.
Click on the Advanced tab and fill in the Redirect URL with https://<URL to Citrix Portal> then click on the Create button to create the virtual server used for redirecting HTTP to HTTPS:
Note that it is normal that the virtual server used for redirecting HTTP to HTTPS has the State listed as being down:
Repeat the same procedure for the website that will be accessed via the internet network:
Configure DNS Servers
While it is possible to use IP addresses to reference servers, it is recommended to use DNS names as much as possible because it makes it easier to modify IP addresses of referenced servers when needed. Note the name servers configured in Traffic Management –> DNS --> Name Servers:
NetScaler Gateway Configuration
Configure LDAP Authentication
Servers
In order to allow the NetScaler to proxy the authentication request with Active Directory credentials between the user and the StoreFront server, LDAP authentication server objects need to be created. Navigate to NetScaler Gateway –> Policies –> Authentication --> LDAP and click on the Servers tab:
Click on the Add… button to create a new authentication server:
Fill in the following in the Create Authentication Server window:
IP Address: The IP address of the domain controller
Port: The port for LDAP (389 is the default)
Base DN (location of users): The distinguish name for the top level OU or container where user accounts are stored. Note that the search is recursive so objects in the sub OUs are also authenticated.
Administrator Bind DN: The UPN of the service account used for searching the Base DN.
Administrator Password: Password for the service account.
Confirm Administrator Pass…: Password for the service account.
The rest of the fields can be left as defaults.
Repeat the same procedure for other domain controllers that are available for authentication:
Policies
Once the authentication server objects have been created, we can proceed with creating the authentication policies for each authentication server by navigating to NetScaler Gateway –> Policies –> Authentication --> LDAP and click on the Policies tab:
Click on the Add… button and fill in the following:
Name: <A name for the authentication server policy>
Server: <Select one of the authentication servers created in the previous step>
The NetScaler allows expressions to be defined to restrict clients authenticating (i.e. whether the client has an antivirus scanner) but the design will not include these restrictions and therefore the only expression defined should be True value which equates to no restrictions:
Repeat the procedure for the other authentication servers:
Configure Virtual Servers
The virtual servers in the NetScaler Gateway node represent the actual portal that users connect to which also authenticates on behalf of the user. As the design of the NetScaler is dual-homed. The interface receiving internet traffic will be used for users authenticating from the internet and the interface facing the internal network will be used for internal users and as the callback site for the StoreFront during the proxy authentication request. With this in mind two virtual servers will need to be configured by navigating to NetScaler Gateway --> Virtual Servers:
Click on the Add… button and fill in the following:
Fill out the following fields as such:
Name: <The name of the portal (in this case a name for the external site)>
IP Address: <The IP address that external internet users will be connecting to>
Assign the SSL certificate that the site will be using.
**For more information about installing an SSL certificate, please see this post:
Generating CSR and installing certificate on NetScaler VPX 1000
http://terenceluk.blogspot.com/2012/10/generating-csr-and-installing.html
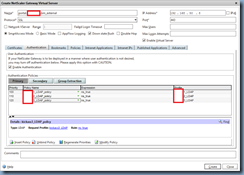
Click on the Authentication tab:
Right click under the Authentication Policies window with Primary selected and select Insert Policy:
Insert the authentication polices that were created earlier:
Note that the priority is incremented by a value of 10 where a lower priority denotes a higher preference:
Click on the Policies tab:
Right click in the Session windows and select Insert Policy:
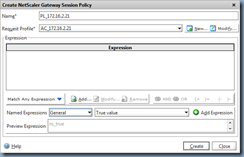
Select New Policy… to create a new policy:
Type in a name for the session policy (this example will use PL_ and the IP of the load balanced virtual server) and click on the New button to create a new Request Profile):
Type in a name for the session profile (this example will use AC_ and the IP of the load balanced virtual server) and click on the New button to create a new Session Profile):
Click on the Client Experience tab, check the Override Global checkbox for Single Sign-on to Web Applications and check the checkbox for Single Sign-on to Web Applications:
Click on the Security tab, check the Override Global checkbox for Default Authorization Action and change the setting to ALLOW:
Click on the Published Applications tab, enable the Override Global settings for:
- ICA Proxy
- Web Interface Address
- Web Interface Portal Mode
- Single Sign-on Domain
Fill in the fields as follows:
ICA Proxy: ON
Web Interface Address: http://portal.domain.bm/Citrix/CitrixWeb
Web Interface Portal Mode: Normal
Single Sign-on Domain: <your internal domain for sign on>
Note that the Web Interface Address URL is the address that is passed to the StoreFront server and portal.domain.bm resolves to the load balanced virtual server IP on the NetScaler (172.16.2.21) which will load balance between the two StoreFront servers. A DNS name is used instead of the actual load balanced IP because this would allow future changes to the load balanced IP as simple as updating the DNS record.
Click on the Create button to create the session profile.
Note that the Request Profile field now has a profile assigned:
Proceed by assigning True value as an expression:
Click the Create button to create the policy and note that the new policy has been assigned to the virtual server with a priority of 100:
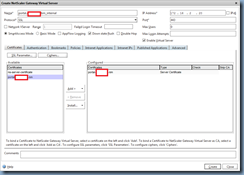
Proceed by clicking on the Published Applications tab:
- http://someDeliveryController1.bm
- http://someDeliveryController2.bm
- http://someDeliveryController3.bm
Note that IPs of the servers are allowed as well but using DNS names allows us to change the IPs of these servers in the future by simply updating the DNS records.
Repeat the process for the other STA servers and click on the Create button to create the new virtual server:
To confirm that the STA servers are reachable, double click on the virtual server that was just created and navigate to the Published Applications tab to verify that the STAs have the State labelled as being up:
Repeat the same procedure for the internal server:
We will be reusing the same policy we created earlier named PL_172.16.2.21 for this virtual server:
- http://someDeliveryController1.bm
- http://someDeliveryController2.bm
- http://someDeliveryController3.bm
Note that IPs of the servers are allowed as well but using DNS names allows us to change the IPs of these servers in the future by simply updating the DNS records.
Confirm that the STA servers are reachable by double clicking on the virtual server that was just created and navigate to the Published Applications tab to verify that the STAs have the State labelled as being up:
StoreFront Configuration
Configure NetScaler Gateway
The reason why we need to configure the NetScaler Gateway node first is because the object created in here will be referenced during the Stores configuration. Click on Add NetScaler Gateway Appliance:
Fill in the following fields:
Display name: <A logical name representing the NetScaler VPX appliance>
NetScaler Gateway URL: <The URL for the StoreFront server to reach the load balanced virtual server configured on the NetScaler (172.16.2.21)>
Version: <Specify the version of the NetScaler appliance>
Subnet IP Address: <The subnet IP (SIP) of the NetScaler appliance>
Logon type: <Select Domain>
Callback URL: <Specify a URL that points to the internal virtual server configured on the NetScaler (172.16.2.20)
Once the NetScaler Gateway has been created, proceed by clicking on Secure Ticket Authority:
Click on the Secure Ticket Authority link on the right hand pane and enter the following STA servers:
- http://CONT01SRV.domain.bm
- http://CONT02SRV.domain.bm
- http://CONT03SRV.domain.bm
Configure Server Group
Ensure that the Base URL is configured as the StoreFront’s server name:
Configure Authentication
Enable the following Authentication Method:
- User name and password
- Domain pass-through
- Pass-through from NetScaler Gateway
Configure Stores
Click on Enable Remote Access:
Configure the following:
Remote access: <Full VPN tunnel>
NetScaler Gateway appliances: <Select the NetScaler Gateway appliance object>
Default appliance: <Select the NetScaler Gateway appliance object>
Configure Receiver for Web
No configuration changes are required for the Receiver for Web node.
Configure Beacons
No configuration changes are required for the Beacon settings.






































































3 comments:
same here. Thanks.
I am using NS10.5 50.9nc, and i can't seem to get section "Configure HTTP to HTTPS Redirect", under advance no option for redirect.
I tried to add another VS with the same ip, but with ssl, but it's always down, even after adding a ssl-cert.
Thanks again.
btw: i am using only one storefront server.
We are the worlds leading publisher of Squid 'Native ACL' formatted blacklists, that allow for web filtering directly with Squid proxy. Of course we also offer alternative formats for the most widely used third party plugins, such as DansGuardian and Squidguard. And while our blacklists are subscription based, they are as a result of our efforts, of a much higher degree of quality than the free alternatives.
We hope to serve you,
--
Signed,
Benjamin E. Nichols
http://www.squidblacklist.org
Post a Comment