Problem
You’ve just used the Skype for Business Server 2015 – Deployment Wizard to request a certificate for the internal interface of the Lync Edge server:
The process completes with warnings:
Viewing the logs displays the following warning:
Warning: The chain of the certificate "CA6EEEC4F50136BCDF70F2A6369C3189F4B7F980" is invalid.
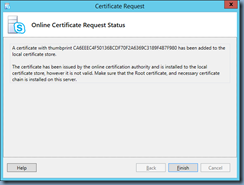
Clicking the Next button displays the following message:
A certificate with thumbprint CA6EEEC4F50136BCDF70F2A6369C3189F4B7F980 has been added to the local certificate store.
The certificate has been issued by the online certification authority and is installed to the local certificate store, however it is not valid. Make sure that the Root certificate, and necessary certificate chain is installed on this server.
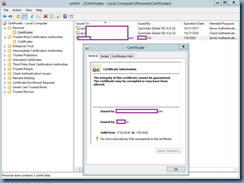
You notice that it is not available to be assigned and launching the properties of the certificate display the following:
The integrity of this certificate cannot be guaranteed. The certificate may be corrupted or may have been altered.
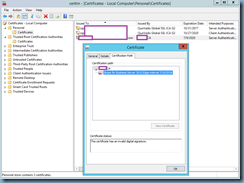
Clicking on the Certification Path tab displays the following Certificate status:
This certificate has an invalid digital signature.
Clicking on the Root CA shows This certificate is OK for the Certificate status indicating there are no issues with the Root Certificate Authority:
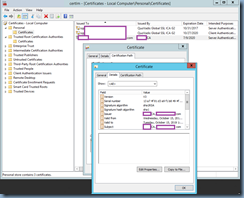
However, opening the properties of the Root certificate displays properties that does not appear to be expected root CA. In this example, I noticed that the Valid from date was incorrect (it appeared to belong to the old root CA’s certificate):
The Signature algorithm and Signature hash algorithm was also incorrect because I had upgraded them to sha256:
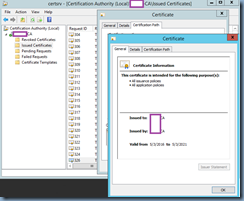
What I did was launch the Certification Authority management console on the root CA and locate the issued certificate:
The properties showed that the status was in a healthy state:
Opening the properties of the root CA certificate confirmed my suspicion that the Skype for Business Edge server is displaying a different root CA as the issuer of the certificate because the Valid from dates were different:
The Signature algorithm and Signature hash algorithm was shown and expected to be sha256:
Solution
One of the causes of such an issue is if you haven’t updated the root certificate in the Trusted Root Certification Authorities on the Skype for Business Edge server:
In this example, the server had the older sha1 certificate but not the newer sha256 so it seemingly decided to display the newly issued certificate as one created by the old CA. To correct this problem, export and import the new sha256 root certificate into the Trusted Root Certification Authorities on the Skype for Business Edge server and the newly issued certificate for the Edge server will be displayed properly so you can assign to the Edge service.












1 comment:
good job! y save my life! Thank!
Post a Comment